Client Reviews
Attorney Reviews: Your Guide to Choosing the Best Legal Representation
Over the years, I have handled hundreds, if not thousands, of cases. Sometimes these former clients say a kind word or two, and I thought I would share a few of those with you who are trying to decide on who can help with your current question or situation. I am so grateful for their allowing me to help.
Why Client Reviews Matter
When searching for an attorney, reviews and testimonials from previous clients can provide valuable insights into the lawyer’s effectiveness, professionalism, and approachability. These first-hand accounts help potential clients make informed decisions about who to trust with their legal issues.
Top Five Things to Consider When Hiring a Lawyer
| Consideration | Description |
|---|---|
| Experience | Look for an attorney with extensive experience in the specific area of law relevant to your case. |
| Reputation | Research the attorney’s reputation in the legal community and among past clients through reviews and ratings. |
| Communication | Ensure the lawyer communicates clearly and promptly, keeping you informed about your case’s progress. |
| Fee Structure | Understand the attorney’s fee structure and ensure it is transparent and reasonable for the services provided. |
| Compatibility | Choose a lawyer who makes you feel comfortable and confident in their ability to represent your interests effectively. |
Benefits of Choosing W. F. Casey Ebsary Jr.
Proven Track Record
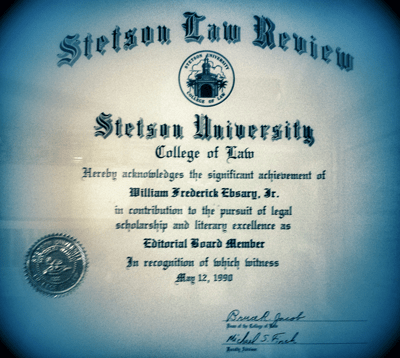
W. F. Casey Ebsary Jr. has successfully handled numerous cases, providing dedicated and personalized legal representation to each client. Whether you are facing criminal charges, dealing with business legalities, or navigating post-college legal issues, Casey Ebsary offers expert guidance and support.
Top Five Reasons to Select W. F. Casey Ebsary Jr.
- Extensive Legal Knowledge: Casey Ebsary possesses deep expertise in various legal fields, ensuring comprehensive legal solutions.
- Personalized Attention: Every client receives tailored legal advice and representation, ensuring their unique needs are met.
- Strong Advocate: Casey is known for his vigorous defense and unwavering commitment to his clients’ best interests.
- Transparent Fees: Clear and reasonable fee structures with no hidden costs, providing peace of mind and financial clarity.
- Accessible and Approachable: Always available to address questions and concerns, making the legal process less intimidating.
Contact Us Today
If you’re seeking reliable legal representation, call W. F. Casey Ebsary Jr. at 813-222-2220 or use our online contact form to schedule a free consultation. We are here to help you navigate your legal challenges with confidence.
Read Reviews and Compare
Selecting the right attorney can significantly impact the outcome of your case. With extensive experience, a stellar reputation, and numerous satisfied clients, W. F. Casey Ebsary Jr. is a top choice for individuals and businesses in need of legal assistance. Don’t hesitate to reach out and see how we can help with your legal needs.
Call W. F. Casey Ebsary Jr. at 813-222-2220 or use our online contact form to schedule a free consultation today. Let us put our expertise to work for you. Choosing an attorney is a critical decision that should not be taken lightly. By considering experience, reputation, communication, fee structure, and compatibility, you can make a well-informed choice. Trust the positive reviews and testimonials from past clients and take the next step towards resolving your legal issues by contacting W. F. Casey Ebsary Jr.
Call W. F. Casey Ebsary Jr. at 813-222-2220 or use our online contact form to schedule a free consultation. Your legal concerns deserve the best possible representation.
The Florida Bar News noted, “Rating sites like Lawyers.com, Avvo, and Yelp require reviewers to pledge honesty, but do little else. That’s frustrating for attorneys who, under most circumstances, are barred by ethical constraints from revealing information about a case without a client’s consent.”




